Source: https://www.linkedin.com/feed/update/urn%3Ali%3Ashare%3A6701686163566080000
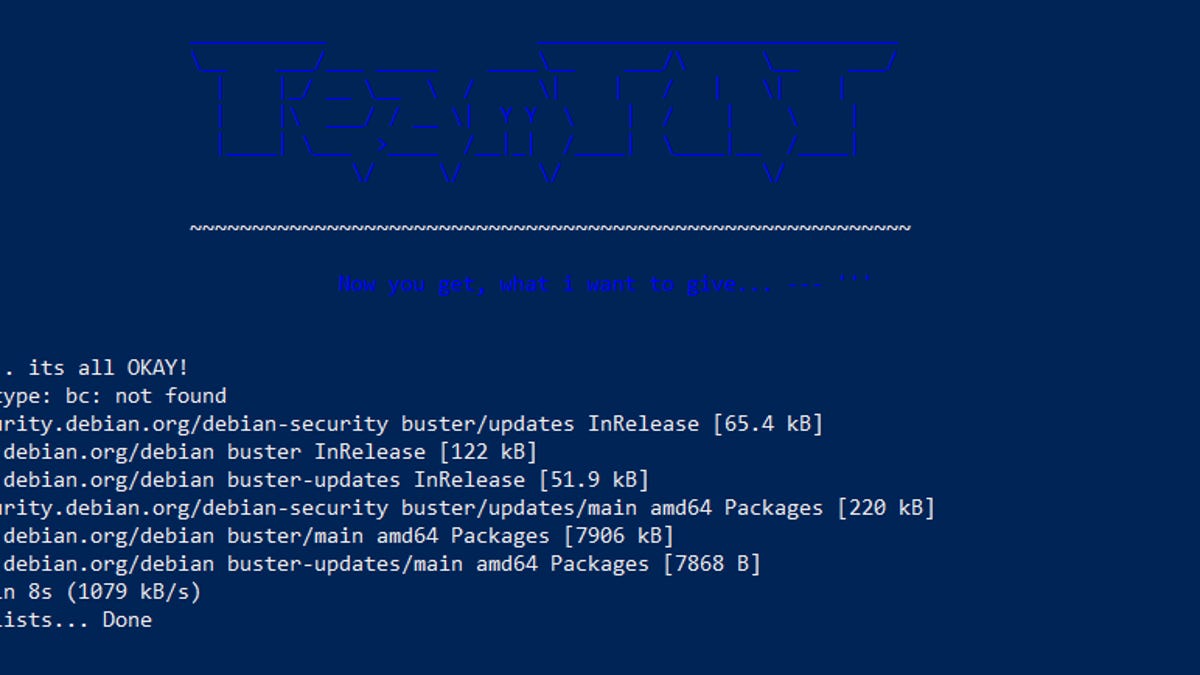
#TeamTNT #Crypto #mining #worm steals #AWS #credentials: #cryptojacking:
https://lnkd.in/eUuQHuN :
#TeamTNT has become the first crypto-minining #botnet to include a feature that scans and steal AWS credentials. It’s the first worm we’ve seen that contains such AWS specific functionality. The worm also steals #local #credentials, and scans the internet for #misconfigured #Docker #platforms. We have seen the attackers, who call themselves “TeamTNT”, compromise a number of #Docker and #Kubernetes systems. These attacks are indicative of a wider trend. As organisations migrate their computing resources to #cloud and #container #environments, we are seeing #attackers following them there.
What to Do: #Countermeasures for Above #Attacks:
Identify which systems are storing AWS credential files and delete them if they aren’t needed.
Use firewall rules to limit any access to Docker APIs. Use a whitelisted approach for your firewall ruleset.
Review network traffic for any connections to mining pools, or using the Stratum mining protocol.
Review any connections sending the AWS Credentials file over HTTP.
United States Air Force Air Force Research Laboratory Ventures:
Global Risk Management Network LLC: Rome, N.Y., USA: USAF-AFRL Ventures: AIMLExchange™, C4I-Cyber™